HTTP vs HTTPS The Technical Difference Explained Between HTTP and HTTPS
HTTP vs HTTPS – what’s more secure? The difference between HTTP and HTTPS is important to understand. HTTP, or Hypertext Transfer Protocol, is the standard protocol that lets users send data between web browsers and servers. HTTPS, or Hypertext Transfer Protocol Secure, is a more secure version of HTTP; it lets users encrypt data sent over between the browser and server so that only its intended recipient can access it. In this blog, we’ll explore the technical differences between HTTP and HTTPS, discuss the role of SSL/TLS certificates, and look at why switching to HTTPS can help keep your website secure.
What is HTTP?
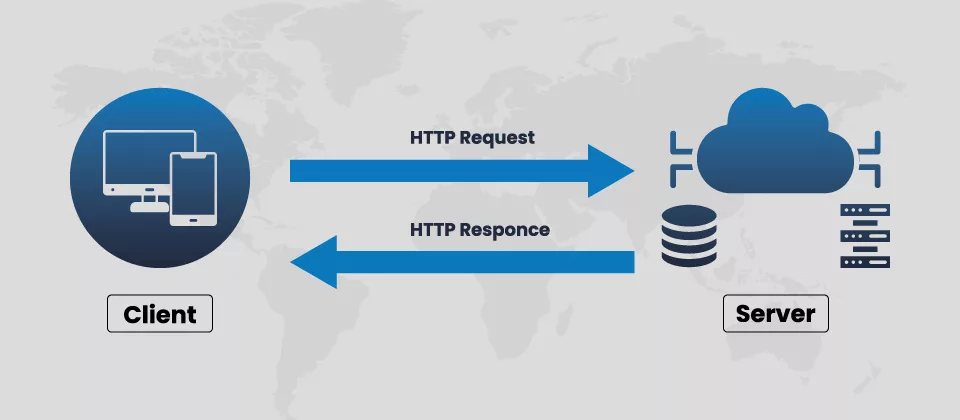
HTTP lets users send and receive data over the internet. It’s an Application-Level protocol or the OSI Model, works on top of the underlying TCP/IP Network Layer, and handles the details of establishing and maintaining connections between devices. HTTP enables web browsers to request resources from web servers and receive responses in return, such as HTML pages or images.
What is HTTPS?
As mentioned above, HTTPS is a secure version of HTTP; it uses SSL certificates to encrypt all the communication between a client & a server. Hence, any data sent over HTTPS is secure, and intended third parties can not intercept that data.
How Does a Typical HTTP Request Work?
When a web browser requests HTTP resources, the request is sent over the internet, which contains information such as the URL of the webpage is requested and the type of data being requested (e.g., HTML page or image). When it reaches the server, it checks if the requested resource exists and returns a response code to indicate whether it succeeded in serving the resource. Upon success, the server sends an HTTP 200 OK response code back to the browser, along with any requested associated content.
If there’s an issue on either end; for example, if a user’s device cannot connect to a website; then an error status code may be sent instead, such as HTTP 404 Not Found.
With HTTP, when the user sends data between the browser and server, it remains encrypted and cyber criminals may try to intercept it using various malicious attacks. Even attackers could use this information to gain access to the user data/take over a user’s account on a website.
What is the Difference Between HTTPS and HTTP?
Now that we’ve discussed the basics of HTTP requests let’s look at the differences between HTTP and HTTPS.
Security
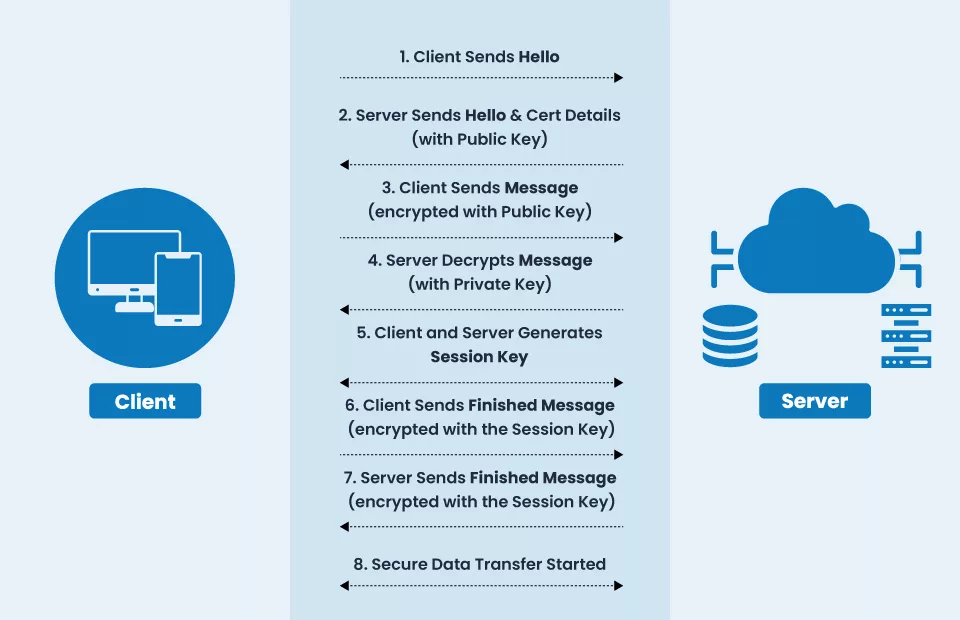
The main difference between HTTP & HTTPS is security; as mentioned above, HTTPS encrypts all the communication between a web browser and server using its strongest 256-bit Public Key cryptography, making it harder for attackers to access confidential information like bank details, passwords or credit card details. The data sent through HTTP is more likely to be easily tampered with or modified due to the absence of encryption or security mechanisms.
Port
Another key difference between HTTP and HTTPS is the port they use. By default, HTTP requests pass over port 80, while HTTPS requests pass over port 443.
Protocol
HTTP and HTTPS are application-level protocols but differ in how they communicate with web servers. HTTP uses an insecure connection to send requests & receive responses from the server, which means there is a big lack of data security. HTTPS uses an encryption mechanism, so all data transmitted between the browser/server remains secure and cyber attackers can not intercept it.
Data Scrambling
HTTP does not include any scrambling of the data; attackers can easily read the data transferred through the HTTP Connection. On the other hand, HTTPS scrambles the data using SSL/TLS certificates and its secure hashing algorithms before sending it out over the Internet. So, cybercriminals can not be able to understand what type of data is being sent or received.
Validating the Domain Name
Domain Name Validation is an important part of enabling the HTTPS connection. It guarantees that the website a user is connected to is legitimate and not malicious. HTTP has no domain name validation system, so users are more vulnerable or easily become targets of attackers.
Search Engine Ranking & SEO
Google and other search engines prioritize websites that use HTTPS over HTTP websites. Hence, switching from HTTP to HTTPS is important if you wish your website to rank higher in the search engine.
SSL Certificate is a must-have measure to boost SEO Ranking.
Speed
In terms of speed, HTTPS has a slight edge over HTTP. Although the encrypted communication between the browser & server takes slightly longer, HTTPS speed is comparatively higher. Even if you take the HTTP vs HTTPS speed test, you will find HTTPS Pages speed is better.
Vulnerability
HTTP is vulnerable to man-in-the-middle attacks & other malicious attacks due to a lack of security mechanism, while HTTPS provides a secure encrypted connection which makes it difficult for attackers to access sensitive data.
Cost
You do not need to pay anything using HTTP protocol on your website, while HTTPS requires an SSL/TLS certificate. Nevertheless, the cost of acquiring & maintaining an SSL/TLS certificate is generally minimal.
Know the Difference between HTTPS and SFTP.
How Does HTTPS Help Authenticate Web Servers?
Along with providing encryption & security, HTTPS also helps authenticate web servers. Authentication is the process of verifying that the server is who it says it is, which helps protect users from phishing & other malicious attacks by confirming that they are connecting to a legitimate website.
HTTPS includes several layers of authentication, such as certificate validation and domain name validation. Once the server has been verified, HTTPS enables an encrypted connection between the browser and server so that all data sent over the connection remains secure.
In the early days of HTTP, architects did not prioritize security; however, it has become paramount in today’s modern Internet era. You must regard the Authentication to remain secure over the internet.
The server uses the Private Key to sign every HTTPS request. This ensures that the browser can trust that the response it gets back is from a legitimate source and not from a malicious actor. By providing authentication, HTTPS helps protect users from malicious actors who seek to gain access to their sensitive data.
Types of Attacks HTTPS Prevent
On-path Attacks:
An on-path attack is an attack type where an attacker poses as one of the endpoints in a secure connection; this allows the attacker to intercept and modify data transmitted between the two endpoints without their knowledge.
Man-in-the-Middle (MITM) Attacks:
A man-in-the-middle attack occurs when attackers insert themselves into a secure connection between two systems and monitor or modify data sent over that connection.
DNS Hijacking:
DNS Hijacking is a type of cyber-attack where the attackers try to redirect the traffic from one domain to another to gain access the sensitive data or maliciously modify it. HTTPS prevents this type of attack by verifying the identity of the server, ensuring that users are connecting to the original website.
BGP Hijacking:
BGP (Border Gateway Protocol) hijacking is an attack in which an attacker takes control of the DNS (Domain Name System) & redirects traffic to malicious IP addresses or domains.
Domain Spoofing:
Domain spoofing is an attack where an attacker creates a fake website with similar website features to the original to deceive unsuspecting users; it can cause serious damage to a website’s reputation.
Types of SSL Certificates Used with HTTPS
An SSL certificate is utilized to encrypt data transmitted between the browser and server. There are three types of SSL certificates available:
Domain Validated Certificate (DV): DV SSL provides basic encryption of 256-bit and is issued once a domain name has been validated, offering instant issuance.
Organization Validated Certificate (OV): Called OV SSL, it is issued after both a domain name and organization have been validated; It provides enhanced encryption and organization authentication. Certificate Authority takes up to 3 days to issue OV SSL.
Extended Validation Certificate (EV): Known as EV SSL, issued after a strict vetting & identity verification process that includes organization and domain name verification. It provides the highest levels of encryption and authentication; CA takes up to 5 days to issue the EV SSL.
Conclusion
Regarding HTTP vs. HTTPS, there is no doubt that HTTPS is the more secure. HTTPS offers strong encryption & authentication, preventing websites and users from the cyber-attacks mentioned above. As a business, it is vital that you deploy SSL certificates in your website server to protect your customers’ data and keep it out of the hands of malicious actors.
