Common SSL/TLS Attacks & Challenges: What SSL Prevents?

Step into the world of cybersecurity with SSL/TLS challenges and the protection they offer against malicious exploits. This illuminating blog will unravel the mysteries surrounding SSL/TLS, exploring their formidable defenses against various attacks.
From the fundamental question of what SSL/TLS prevents to delving into the most common attacks thwarted by these protocols and even deciphering the intricate workings of SSL in preventing dreaded Man-In-The-Middle attacks – we’ve got it all covered.
Additionally, we’ll discover the vulnerabilities that could compromise TLS connection security. Brace yourself for a comprehensive exploration that promises to enrich your SSL/TLS knowledge, and stay with us until the very end to unlock the full spectrum of insights.
What Attacks does SSL/TLS Control?
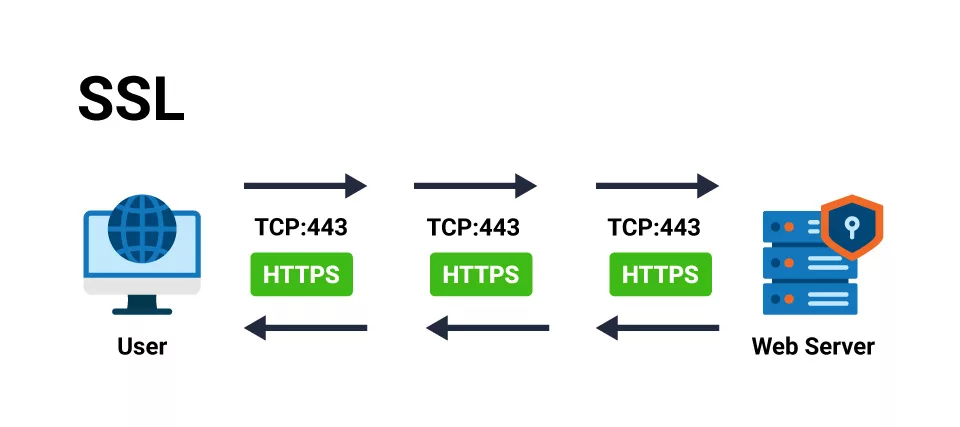
SSL and TLS, encryption protocols for securing communication channels between network devices, play a crucial role in safeguarding data and preventing attacks.
These protocols establish secure connections by binding the identities of systems, users, websites, and more through digital certificates. These certificates can be issued either by trusted internal certificate authorities within an enterprise or by public certificate authorities that are globally recognized.
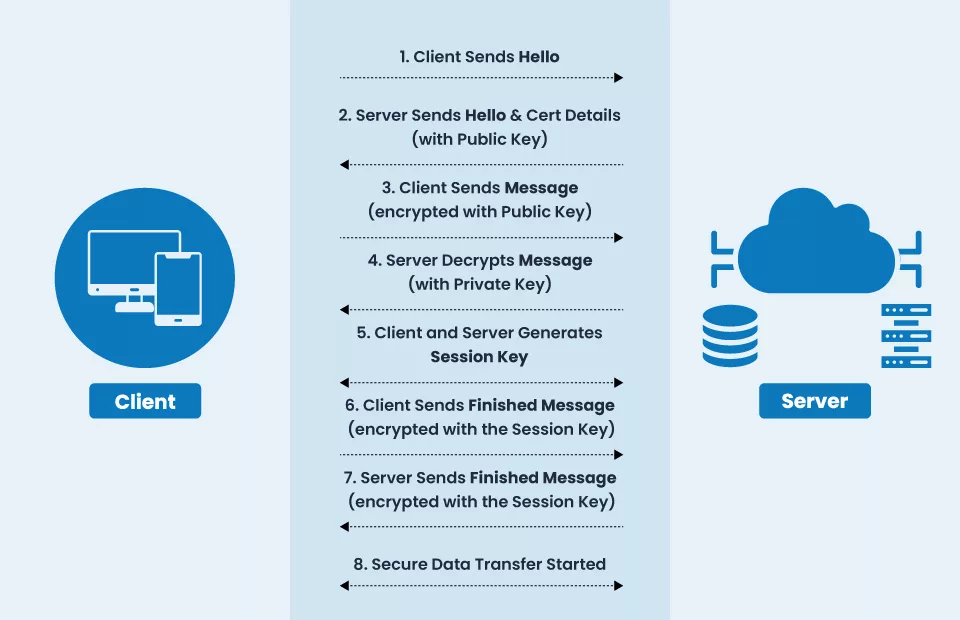
These certificates store the identities of end entities and contain a cryptographic key pair consisting of a public key and a private key.
The public key is openly distributed along with the certificate, while the private key is securely held by the entities involved in the communication. When network devices communicate, this essential pair encrypts the transmitted data, ensuring the information remains protected from tampering or alteration during transit.
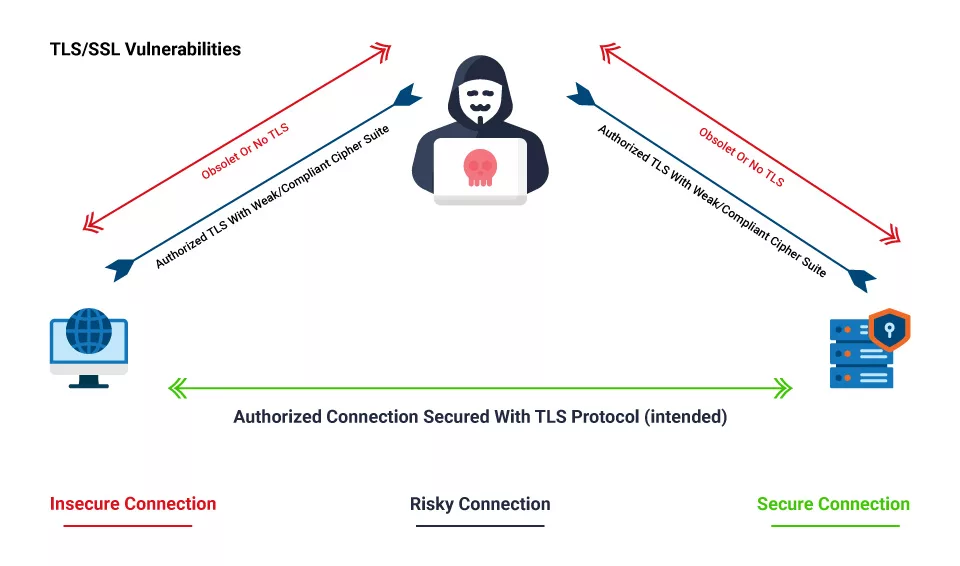
Despite the robust security mechanisms provided by SSL/TLS, there are still potential vulnerabilities and gaps in technology and processes that hackers can exploit to compromise the security of these encrypted connections.
This blog post will explore some standard SSL/TLS challenges and vulnerabilities attackers may exploit. Understanding these potential weaknesses is essential for maintaining the integrity and security of data in transit.
What Digital Threats Can SSL Prevent?
SSL/TLS is the cornerstone of internet and online security, serving as the de facto standard for safeguarding digital communication. These protocols play a pivotal role in encrypting data, traversing the uncharted territories of the internet, and forging a protective shield between client machines and servers (the bastions of websites and online services).
This encryption prowess is not just a mere technological marvel; it is the guardian that repels many potential attacks.
Even if a hacker were to intercept encrypted data in transit cunningly, they would find themselves clutching a cryptographic enigma, impenetrable without the elusive private key designed for the decryption ritual. This impenetrable layer of defense forms the bedrock upon which SSL/TLS builds its reputation for digital fortitude.
The very essence of SSL/TLS lies in its capacity to cocoon websites in a protective embrace, rendering them resistant to the evil forces that seek to steal, alter, or impersonate. While achieving absolute security in the digital remains elusive, websites entrusted with sensitive customer data recognize the importance of enabling SSL/TLS. Doing so bolsters their defenses, enhancing customer confidence and fostering a more secure online environment.
Yet, the cyber threats refuse to stand still. Hackers, driven by their insatiable quest for breaching the fortifications of the internet’s de facto standards, persistently probe the boundaries of SSL/TLS. The irresistible allure of SSL/TLS vulnerabilities fuels their determination, placing organizations at the precipice of potential breaches and unforeseen system downtime.
Most Common SSL and TLS Attacks
SSL and TLS are critical cybersecurity protocols, serving as authentication and encryption for data transmission. TLS, short for Transport Layer Security, is the evolutionary successor to the SSL (Secure Socket Layer) protocol.
Currently, TLS 1.3 emerges as the shining beacon of security in secure communication, outshining its predecessors regarding robustness and reliability. This commendable protocol is meticulously detailed in RFC 8446, setting the gold standard for secure data transmission.
However, the path to TLS 1.3’s supremacy was not without its trials and tribulations. SSL and TLS versions 1.2 found themselves on the wrong side of security vulnerabilities and attacks, leading to their eventual deprecation.
Notable threats such as ROBOT, LogJam, and WeakHD exploited weaknesses in how key exchanges unfolded during the negotiation phase between clients and servers. While TLS 1.2 represented an improvement by mitigating some of these vulnerabilities, it still harbored susceptibility to cunning downgrade attacks, as exemplified by the notorious POODLE attack.
The introduction of TLS 1.3 marked a transformative moment in cybersecurity. This latest iteration took significant strides in fortifying the handshake process during client-server negotiations, effectively thwarting the vulnerabilities that had plagued its predecessors.
TLS 1.3 emerged as the beacon of hope, safeguarding the integrity and confidentiality of data exchanges in an increasingly interconnected digital world.
Here, we’ll delve into some common SSL attacks, shedding light on their mechanisms and potential risks:
SSL/TLS Downgrade Attacks:
These attacks deceive web servers into negotiating connections using older, insecure versions of TLS. Attackers then attempt to intercept or alter information by exploiting weaknesses in outdated protocol versions or cryptographic algorithms.
Poodle Attack:
The POODLE attack targets communications encrypted with SSLv3 and can steal confidential data like passwords and session cookies. Configure your webserver to support TLS 1.2 or higher protocols to mitigate this attack.
Freak Attack:
FREAK exploits export cipher suites with weak 512-bit or less RSA moduli, originally designed to comply with export regulations. To safeguard your website, disable support for export-grade cipher suites.
Logjam Attack:
This attack downgrades the connection to 512-bit export-grade Diffie-Hellman groups. Disabling support for export-grade Diffie-Hellman cipher suites on your servers can thwart Logjam attacks.
SSL Renegotiation Attack:
SSL Renegotiation attacks exploit vulnerabilities in the SSL renegotiation procedure, allowing attackers to inject plaintext into a victim’s requests. While they cannot decrypt the client-server communication, attackers can add their requests to the conversation.
To address this vulnerability, SSLv3 can stop allowing renegotiation on the server side, or a renegotiation indication extension can be employed in TLS.
Drown Attacks:
DROWN is a critical vulnerability targeting servers supporting contemporary SSL/TLS protocol suites by exploiting their support for obsolete and insecure protocols. It allows attackers to break encryption, potentially accessing sensitive communications. To counter DROWN attacks, ensure private keys aren’t used with server software allowing SSLv2 connections.
Sweet32 Attack:
Sweet32 exploits 64-bit block ciphers in CBC mode using a “birthday attack.” Attackers capture enough traffic via man-in-the-middle attacks or malicious JavaScript to execute the attack. Protect against Sweet32 by avoiding legacy 64-bit block ciphers and disabling cipher suites that use DES/3DES.
Truncation Attack:
In a TLS truncation attack, logout requests from victims are blocked, keeping them unknowingly logged into a web service. An attacker injects an unencrypted TCP FIN message to close the connection, and the server remains unaware of the abnormal termination. SSLv3 onward employs a closing handshake to prevent this issue.
Understanding these SSL/TLS attacks and implementing appropriate countermeasures is vital for enhancing the security of online communication and safeguarding sensitive data.
How Does SSL Prevent Man-In-The-Middle Attacks?
SSL (Secure Sockets Layer) is pivotal in thwarting the menacing threat of Man-in-the-Middle (MITM) attacks, safeguarding the sanctity of secure communications. Let’s explore how SSL is a stalwart defender against this nefarious breed of cyberattacks.
At their core, MITM attacks involve an intruder cunningly infiltrating the secure communication channel between the sender and the intended receiver.
These attackers employ a variety of tactics to achieve their sinister objectives, and SSL’s arsenal is primed to counter them.
Protection through Private Keys:
SSL offers a primary safeguard through its private keys. These keys are the linchpin that binds the certificate’s authenticity to the endpoints engaged in the secure communication. SSL/TLS private keys are closely guarded, making them exceptionally challenging for hackers to acquire. Without these private keys, attackers are left in the dark, unable to decipher the encrypted data between the sender and receiver.
Intermediate Certificate Authorities (CAs):
In some instances, hackers may attempt to compromise poorly secured Intermediate Certificate Authority private keys. Such breaches can have far-reaching consequences, affecting all certificates issued by these compromised authorities.
However, SSL’s robust security mechanisms are designed to thwart such attacks, making it arduous for attackers to tamper with or intercept the trust established through SSL/TLS certificates.
Root CA Certificate Trust:
SSL also relies on a trusted root authority list that holds certificates from trusted Certificate Authorities. This prevents attackers from surreptitiously inserting fake Root CA certificates into the trusted list. Any such attempt would be swiftly detected and invalidated, maintaining the integrity of secure connections.
Certificate Lifecycle Management:
The importance of managing certificate lifecycles cannot be overstated. SSL ensures that certificates are continually monitored, revoked when compromised or expired, and renewed promptly. This diligent oversight minimizes the risk of attackers leveraging revoked certificates to establish trust with compromised sites and eavesdrop on secure communications.
SSL is a formidable guardian against the insidious Man-in-the-Middle attacks. By safeguarding private keys, fortifying Intermediate CAs, maintaining trust in the root authorities, and meticulously managing certificate lifecycles, SSL erects an impenetrable barrier that thwarts the most determined attackers, preserving the confidentiality and integrity of secure channels.
TLS Connection Cryptographic Protocol Vulnerabilities
SSL/TLS protocols, revered for their role in securing online communications, are not immune to vulnerabilities. Below are the key attacks affecting SSL/TLS versions 1.2 and older, shedding light on the threats and countermeasures:
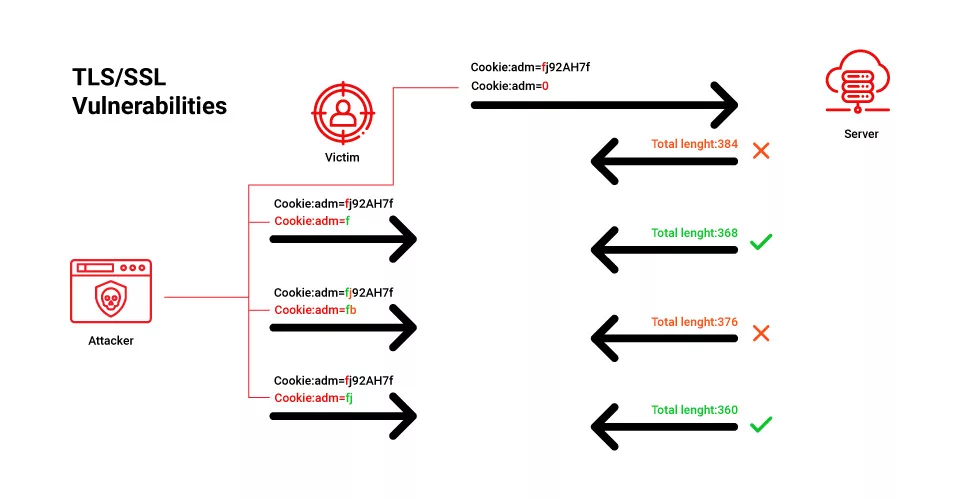
CRIME Attack (Compression Ratio Info Leak Made Easy):
- Vulnerability (CVE-2012-4929): Exploits compression algorithms in TLS.
- Attack Method: Compression methods, like DEFLATE, are utilized to minimize bandwidth requirements. Attackers exploit replacing repeated byte sequences with pointers, deducing sensitive information.
- Countermeasure: Enhance security using browsers supporting the latest TLS protocol, TLS 1.3.
BEAST Attack (Browser Exploit Against SSL/TLS):
Targeted Versions: SSL 3.0 and TLS 1.0
Vulnerability (CVE-2011-3389): Exploits a flaw in the CBC (cipher block chaining) implementation in TLS 1.0.
Attack Method: In a Man-in-the-Middle (MITM) setup, attackers inject crafted packets into TLS streams, decrypting encrypted data. The initialization vector is guessed, and results are compared to decrypt desired data.
Countermeasure: Employ browsers supporting TLS 1.1 or higher to mitigate this attack’s prerequisites and strengthen security.
HEARTBLEED Attack:
Target: OpenSSL library’s heartbeat extension
Vulnerability (CVE-2014-0160): Uncovers flaws in the heartbeat extension.
Attack Method: In a heartbeat message exchange, the server responds with random data from its memory if the client sends a fake data length. This may include critical information such as private keys and credit card details.
Countermeasure: Protect your infrastructure by upgrading to the latest OpenSSL library version or recompiling the installed version with the “DOPENSSL_NO_HEARTBEATS” flag.
BREACH Attack (Browser Reconnaissance and Exfiltration via Compression of Hypertext):
- Target: HTTP compression (not TLS)
- Vulnerability (CVE-2013-3587): Exploits HTTP compression mechanisms.
- Attack Method: Redirects a client’s browser traffic to a third-party TLS-enabled URL, intercepting server-client traffic through MITM techniques. Vulnerable web servers reveal user input/secrets in HTTP response bodies.
- Countermeasure: Disable HTTP-level compression, segregate secrets from user inputs, and employ masking techniques to thwart this attack.
How to Safeguard Your Cyberspace with SSL Certificates?
Securing your enterprise against SSL attacks is paramount in today’s digital landscape. Protecting sensitive data and maintaining the trust of your users requires a strategic approach. Here are some key steps and considerations to bolster your defenses:
Avoid Self-signed Certificates:
Self-signed certificates lack the validation of trusted Certificate Authorities (CAs). Choose certificates from reputable CAs for enhanced security.
Avoid Unknown Certificate Authorities:
Ensure certificates come from recognized and trusted CAs to prevent potential vulnerabilities associated with unknown or untrusted sources.
Avoid Expired SSL/TLS Certificates:
Regularly monitor and renew SSL/TLS certificates to prevent lapses in security. Expired certificates can expose your network to attacks.
Enforce Strict SSL Configuration:
Implement SSL/TLS configuration settings to ensure that only secure cipher suites and protocols are used. This helps protect against vulnerabilities associated with weak encryption.
Monitor Encrypted Traffic:
Be careful against attackers who may exploit encrypted communication for malicious purposes. Implement traffic inspection solutions to detect anomalies and potential threats within encrypted data streams.
Educate Against Phishing Attacks:
Phishing attacks often leverage SSL/TLS encryption to appear legitimate. Educate your employees and users about recognizing and reporting phishing attempts to mitigate this threat.
Comprehensive Security Tools:
Invest in comprehensive security solutions and tools that align with your enterprise’s security goals. This may include intrusion detection systems (IDS), intrusion prevention systems (IPS), firewall solutions, and advanced threat detection.
Regular Security Audits and Updates:
Conduct regular security audits and assessments to identify vulnerabilities and ensure your security measures remain effective. Keep all security tools and software up to date to patch known vulnerabilities.
Incident Response Plan:
Develop and maintain an incident response plan to handle security breaches effectively. Timely responses can limit damage and protect sensitive data.
Employee Training and Awareness:
Train employees to recognize and respond to security threats, including SSL attacks. Establish a culture of cybersecurity awareness within your organization.
Third-party Assessment:
Consider third-party professional cyber security services and penetration testing to evaluate your security posture objectively.
