TLS 1.3: Everything you Need to Know
The ability to provide secure data transfers and convey information over the internet without having it interfered with, altered, used illegally, or read by anyone other than the intended users has become a significant concern for many electronic commerce and online organizations in today’s digital era. These worries have made it necessary to upgrade a variety of internet security mechanisms.
The TLS 1.3 update, which represents a significant step from the transport layer security protocol (TLS) and secure sockets layer (SSL) encryption protocols, is an essential advancement over the current security standard.
The upgraded version was created to avoid exposing the flaws and vulnerabilities present in other previous versions of encryption, and it was approved by the Internet Engineering Task Force (IETF). Numerous advantages of TLS 1.3 include a clear protocol flow, better cryptographic primitives, and increased speed and performance.
TLS 1.3 and its advantages will be thoroughly explained in this article. Let’s first discuss the Transport Layer Security Protocol (TLS) before moving on.
What Is Transport Layer Security Protocol (TLS)?
The term “TLS,” or transport security protocol, refers to the cryptographic protocols that enable secure internet connections. TLS makes data security and privacy for conversations across a computer network easier.
TLS was created from SSL and is frequently used in place of TLS. Every website and certain online services use HTTPS, an application of TLS encryption built on top of the HTTP protocol. Web applications are protected from hazards like DDoS attacks and data breaches with the help of the transport layer security encryption protocol.
The goal is to stop an intermediary from accessing the current packets and obtaining sensitive information (such as usernames, passwords, financial information, personal material, etc.) since cryptographic encryption ensures all data is unreadable to outsiders.
What is TLS 1.3 Encryption?
TLS 1.3 is the internet’s most widely used security protocol, which encrypts data to create a secure mode of communication between two endpoints. TLS 1.3 strives to encrypt as much of the handshake as feasible, replaces outdated cryptographic techniques, and improves security over earlier versions.
TLS 1.2 vs TLS 1.3: What are the Main Differences?
The Internet Engineering Task Force (IETF) defined the TLS protocol, which has undergone several versions. Most web browsers have used the TLS 1.2 protocol, the most recent version of TLS, for the past eight years.
TLS 1.2 was described in RFC 5246. The TLS 1.3 specification had 28 drafts before being finalized on March 21st, 2018. The final iteration of TLS 1.3 has since been published (RFC 8446) as of August 2018
TLS 1.3 delivers many improvements over earlier versions, with the fastest TLS handshake and the most simple, secure cipher suites. TLS handshake efficiency is increased via zero-round-trip-time (0-RTT) key transfers. These modifications strengthen security and improve performance when taken together.
Browsers and operating systems are responsible for adding support for new versions of protocols when they are released. Therefore, they are incentivized to do so; operating systems and browsers should all strive for increased performance and security.
However, it may take time until new protocols are widely supported, mainly as private companies and customers might be cautious about utilizing the most recent browsers, apps, and operating systems.
What Benefits Come with Utilizing the Most Recent TLS Version?
Choose TLS 1.3 if you’re creating an application and need help deciding which TLS version you should use. Significant advancements in the most recent TLS version include:
Zero Round-Trip Time (0-RTT)
Client application data, also known as 0-RTT data, can be sent to the Server after the ClientHello message and has zero round-trip time by the TLS 1.3 protocol.
The time to the first byte on a TLS connection can be lowered using TLS 0-RTT, commonly called “TLS early data” In contrast to TLS 1.2 and earlier versions, TLS 1.3 only needs one RTT (single round trip) of the protocol.
A Quicker TLS Handshake
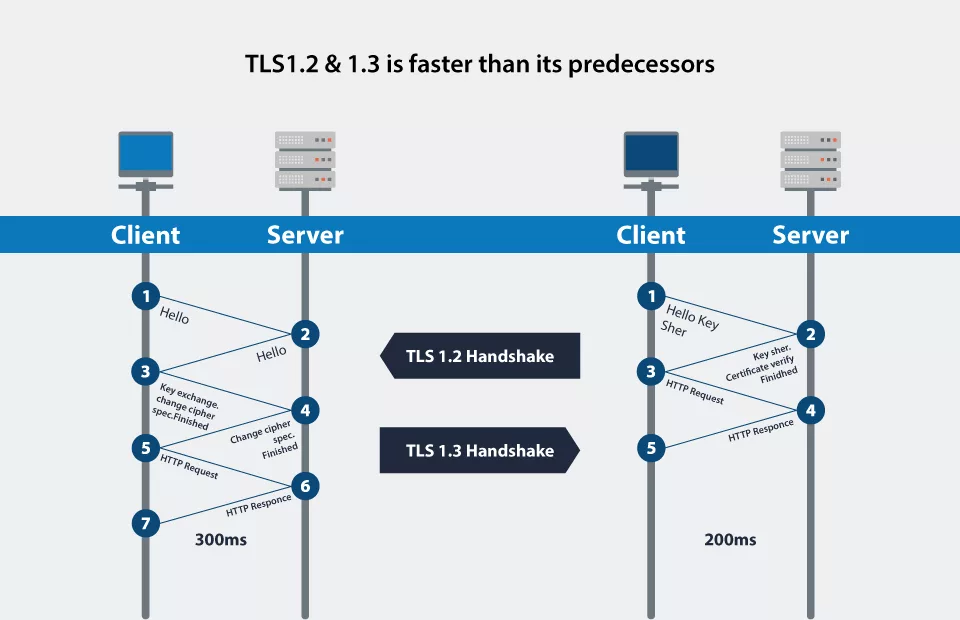
TLS encryption and SSL decryption slow down network connections by adding latency and requiring CPU resources. The initial handshake required encryption and decryption under TLS 1.2 since it was conducted in plain text.
Recommended: SSL/TLS Handshake: A Crucial Step Towards Secure Connections
Given that a handshake typically included 5–7 packets being transmitted between the client and server, this significantly increased connection overhead. With the introduction of server certificate encryption in version 1.3, a TLS handshake may be finished in 0–3 packets, decreasing or eliminating this overhead and enabling more rapid and more responsive connections.
Robust and Better Cipher Suites
Version 1.3 has reduced the size of the encryption cipher suites and lowered the number of packets that must be sent during the TLS handshake.
Using ciphers with cryptographic weaknesses presented possible security issues in TLS 1.2 and older versions. Only algorithms that do not enable Perfect Forward Secrecy (PFS) that are known to be secure are supported by TLS 1.3.
The update also removed the “renegotiation” mechanism, which allows a client and Server with a TLS connection to negotiate new parameters and create new keys. Renegotiation could increase risk.
TLS 1.3’s Enhanced Security
TLS 1.2 has a significant weakness: it is frequently not configured correctly, leaving websites open to attackers.
From TLS 1.2, the following features have been removed by TLS 1.3 because they are no longer necessary or secure: AES-CBC, MD5, SHA-1, RC4, DES, and 3DES, Arbitrary Diffie-Hellman groups — CVE-2016-0701. It is less probable for administrators and developers to misconfigure the protocol because it has been considerably simplified.
Google has begun informing consumers in the search console that they are switching to TLS version 1.2 since TLS version 1 is no longer considered secure. This scenario is another example of Google raising the bar. March 2018 has been set as the ultimate deadline.
Ultimate Advance Secrecy
Perfect forward secrecy is a characteristic of SSL/TLS that prohibits an attacker from being able to decode the data from previous or future sessions if they are successful in stealing the private keys used in a specific session.
Forward secrecy is likely to protect against cybercriminals who put in a lot of effort to see or steal data that has already been sent between a client and Server using a compromised private key. Unique session keys are used for forward secrecy and are regularly and automatically produced. Encrypting the data received during the handshake and decrypting it prevents an attacker from getting the session key.
TLS 1.3’s Browser Support
Since Chrome 65, a draft of TLS 1.3 has been delivered by Chrome. TLS 1.3 final was made available for outbound connections in Chrome 70, which was made public in October 2018.
In Firefox 52 and later (including Quantum), a draft version of TLS 1.3 was made available. Before learning more about server tolerance and the 1.3 handshake, they were still using a risky fallback to TLS 1.2. The most recent TLS 1.3 version was preloaded in Firefox 63, released in October 2018.
TLS 1.3 is enabled by default in Safari 12.1 on macOS 10.14.4, and Microsoft Edge began supporting it with version 76.
Difference Between TLS 1.2 and TLS 1.3:
| S.No | TLS 1.2 | TLS 1.3 |
| 1 | There are several in-and-out messages between the client and server in TLS version 1.2. | While TLS version 1.3 tries to shorten the handshake procedure’ duration by minimizing the number of messages sent to and from between the Client and the Server |
| 2 | The Cipher suites in TLS version 1.2 are less secure. | However, TLS version 1.3, offers Cipher suites that are more secure. |
| 3 | The TLS handshake in TLS version 1.2 is slower. | While the TLS handshake in version 1.3 is quicker |
| 4 | The performance and user experience of the website are poor. | The user experience and website performance are both better. |
| 5 | The connection is a bit slower and less responsive. | However, the connection is faster and more responsive. |
| 6 | Its round-trip time (RTT) is not zero. | While; its round-trip time (RTT) is zero. |
Due to numerous benefits of the TLS 1.2 protocol, such as enhanced performance, security, and zero round trip time, the TLS 1.3 protocol is more likely to be utilized in today’s world.
Conclusion
Although TLS version 1.2 is still in use, there is a growing trend towards TLS version 1.3 because of the version’s ease of use, enhanced performance, data privacy, and security. TLS 1.3 offers a quicker connection, lowering latency when adequately implemented. The speed and user experience of websites are enhanced by reduced latency.
Client-server communications can be made considerably secure by eliminating vulnerable components, simplifying cipher suites, and other weaknesses in security. Organizations should consider maintaining both versions for secure data transfers with legacy systems and apps for a while because TLS 1.3 is not backward compatible with TLS 1.2.
The upgrade from TLS 1.2 to TLS 1.3 is a significant leap. However, choosing to update is simple if your organization wants to increase client confidence while enhancing website performance and security.
FAQ’s
How is TLS 1.3 Work?
Each session in TLS 1.3 begins with a brief key exchange. There will be no impact on earlier sessions if a server is hacked. After exchanging ephemeral public keys, key exchange is completed, and new keys can be generated.
Does TLS 1.3 Encrypt the Certificate?
When server certificate encryption became the default in version 1.3, a TLS handshake could be completed in as few as three packets, lowering or eliminating this cost and enabling quicker, more responsive connections.
Why is TLS 1.3 More Rapid?
On the other hand, the TLS 1.3 handshake only needs one round trip from both sides. As a result, HTTPS connections are quicker and more responsive, and the whole setup time has been reduced in half. In addition to improving website speed, faster connections significantly improve user experience.
Does TLS 1.3 use AES?
Every TLS 1.3 implementation must use AES-128-GCM-SHA256. However, AES-256-GCM-SHA384 and CHACHA20-Poly1305-SHA256 are also recommended.
Why doesn’t TLS 1.3 use RSA?
All static (non-PFS) key exchanges and RSA have been removed in TLS 1.3, however ephemeral Diffie-Hellman keys are still used.
