What Is a CA (Certificate Authority) ? Role, PKI Trust Hierarchies

A certificate authority is something you use each time to access a website that begins with HTTPS. But how can a CA improve the security of your transactions and communications, and what precisely is a CA?
The internet cannot function without certificate authority (CA). Because the internet wouldn’t be secure without CAs, you wouldn’t be able to make purchases, pay taxes, or perform financial transactions online. (Your web browser is now utilizing a certificate authority.)
But precisely what is a certificate authority? What is the purpose of a certificate authority? How do certificate authorities work?
Let’s explore!
What exactly Is a Certificate Authority (CA)?
A certificate authority is a reputable organization that validates websites and other organizations. This allows you to know with whom you are dealing with. They seek to increase the security of the internet for both businesses and individual users. They are crucial to the security of the digital world.
It issues digital certificates for websites and other businesses. Web browsers like Chrome, Safari, and Firefox trust TLS/SSL certificates issued by CAs because they verify a website domain and, depending on which type of certificate, the ownership of the website. To increase confidence in online interactions and transactions, CAs assist in making the internet secure by authenticating websites.
Recommended: Everything to Know About Certera Certificate Authority
What Is the Actual Role of Certificate Authorities (CAs)?
A Certificate Authority (CA) is an organization that issues digital certificates to boost confidence in digital communications and transactions.
A CA’s responsibility is to certify an individual or organization’s identification and issue a certificate that associates the entity’s identity with a public key.
The security of their infrastructure must be maintained, and certificates must be issued according to industry norms and best practices.
They also uphold the validity of the certificate by revoking expired certifications.
By providing certificates for use by others, certificate authorities, which are autonomous organizations, serve as trustworthy third parties. Before issuing a certificate, a certificate authority must verify the legitimacy of the individual or organization initiating the request. Information about the certificate is stored in a repository that is open to the public once issued. Users can verify the status and authenticity of any certificates by accessing the repository.
Certificate authorities issue different degrees of security certificates for different uses. Consider this:
- The Customer Verification
- Secure Email
- Server Verification
Certificate authorities also charge a nominal fee to undertake the verification procedure and provide a credential to interested entities. To validate the legitimacy of businesses, websites, and domain names and to issue digital certificates, CAs thoroughly examine these organizations.
Certificate revocation lists, which show when certificates become invalid before their expiration dates, are also kept up to date by certificate authorities, who also keep track of the status of certificates.
A TLS/SSL certificate from a CA is required for any website that wants to implement HTTPS and show the secure padlock. The information provided by the certificate requester, such as site ownership, name, location, and more, will be verified by the CA before a certificate is issued.
To guarantee that every CA follows the same procedures for validation, CAs must abide by strict industry standards. The standards for TLS encryption and digital certificates are determined by the CA/Browser Forum, which comprises significant browsers and CAs.
How Does a Certificate Authority Work?
The following describes how to ask a certificate authority to issue a signed certificate:
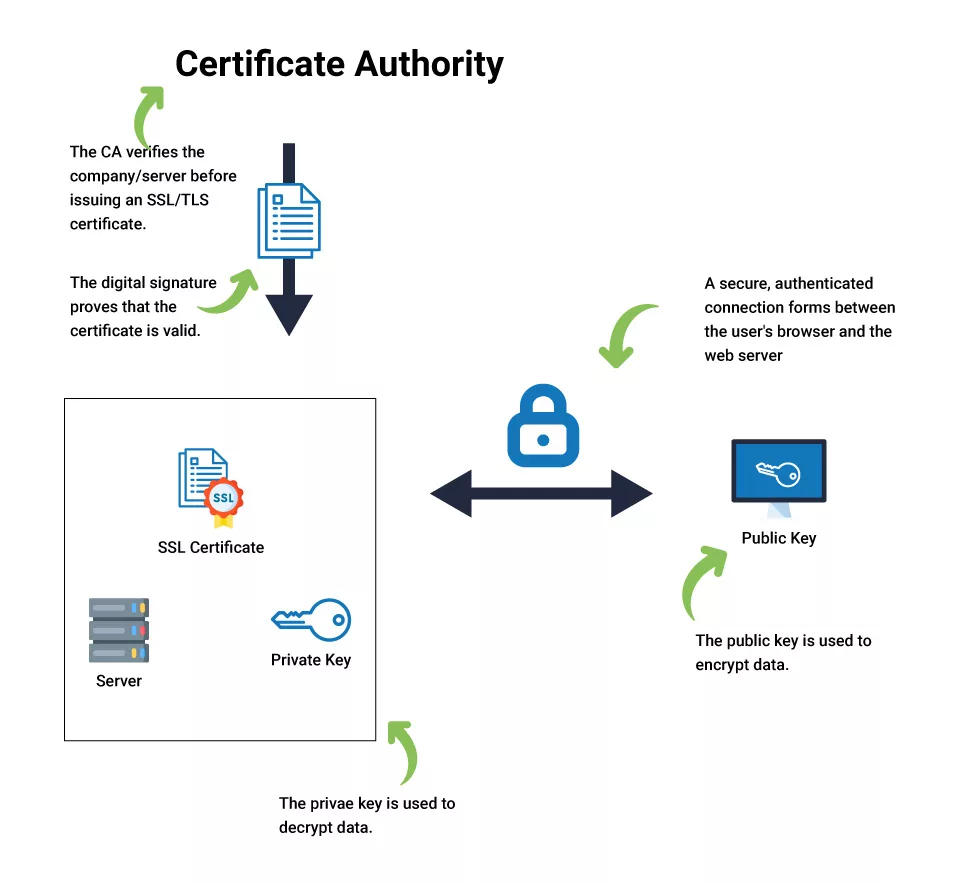
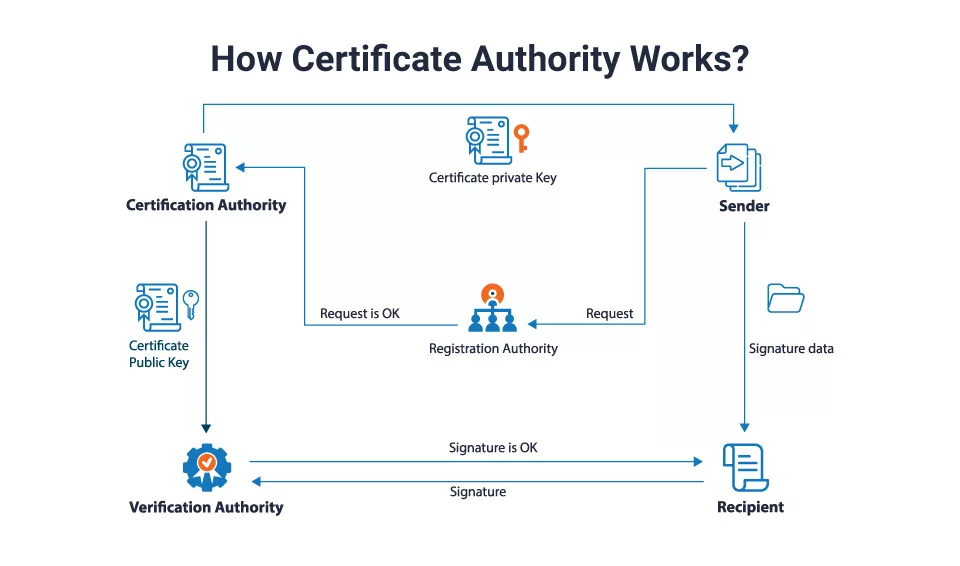
- A certificate signing request (CSR) is sent to a reputable certificate authority by the requestor or client along with a key pair (public and private key). The CSR includes the client’s public key and all the requestor’s data.
- The CA verifies the accuracy of the data on the CSR. If so, it issues a certificate, signs it with the CA’s private key, and then provides it to the requestor for their use.
- The requester can use the suitable security protocol with the signed certificate.
What Procedure is Involved in Authenticating an Organization?
Many certificate authorities use the following procedures to verify the legitimacy of an organization, domain name, or website:
Perform Verification:
Checking the organization’s legitimacy by requesting a digital certificate constitutes the first step in the authentication procedure. Typically, the identification of the applicant is thoroughly examined by certificate authorities. Depending on what type of certification the applicant requests, the check’s nature could often alter. Here are some typical methods of verification:
Domain Validation:
In this essential verification, the certificate authority ensures the applicant is a genuine website or domain owner. The applicant can accomplish this using a verified email address, HTTP/HTTPS file verification, or DNS verification.
Recommended: Domain Validation Process to Issue DV Certificates
Organization Validation:
During this procedure, the certificate authority checks the domain name or website and the company itself. To ensure the authenticity of the organization, validation is frequently required using documents and third-party sources.
Recommended: Organization Validation Process to Issue OV Certificates
Extended Validation:
This sort of verification is the most extensive type, which can take many days. The certificate authority investigates the applying organization in tremendous detail.
Recommended: Extended Validation Process to Issue EV Certificates
Generating Digital Certificates
Three different digital certificates certifying authorities can issue:
Secure SSL Certificate
Secure Sockets Layer (SSL) certificates, sometimes called Transport Layer Security (TLS) certificates, authenticate websites and secure user information. This is accomplished by data encryption using the TLS/SSL handshake, a procedure that secures communication between a web server and a web browser. TLS/SSL certificate-protected websites display HTTPS and a secure padlock indication in the browser address bar.
Cheap SSL Certificates Start at Just $3.99/Year
Code Signing Certificate
This digital certificate provides a signature when software or data are downloaded from the internet. It is the individual who develops the software or publishes the file who signs it, certifying that it is authentic.
Consumers frequently check for a code signing certificate when downloading a product to ensure it hasn’t been tampered with by external factors like viruses. This kind of authorization benefits developers or publishers that sell their products on third-party websites.
Cheap Code Signing Certificates Start at Just $199.99/Year
Client Certificate
A user can identify and validate another user using a client certificate called a Digital ID. As an illustration, the sender of an email could digitally sign it before the recipient validates it on their end.
Client/Email Signing Certificates Start at Just $12.99/Year
Similarly, a machine can utilize this credential to authenticate another machine, just as a user can use it to identify and verify a computer. Two-factor authentication is another application for this digital certificate; it’s frequently used to access restricted databases and make payments.
Once the user inputs their credentials, the device or system verifies.
Verifying the Certificates’ Validity
Each digital certificate has a different duration during which it is valid. For Instance, SSL certificates are good for slightly over a year, but code-signing certificates can be valid for up to three years.
After conducting a thorough background check on a candidate and issuing them certification, the last action certificate authorities take is to check the certification’s validity. A company’s approval can be revoked for a variety of reasons, such as:
- Not adhering to policy standards
- publishing fabricated documents
- Misrepresenting the behavior of software
- Private key lost or stolen.
- Incorrect certificate issued by the certifying body.
A certifying authority updates its certificate revocation list when it revokes a company’s certificate before its expiration date. All digital certificates that the certificate authority revokes before their purported expiration dates are included in this list.
What is the Certificate Chain of Trust?
A trust relationship model, commonly called the “certificate chain of trust,” is the foundation for the SSL/TLS internet security standard. x.509 digital certificates give users a secure and reliable platform to connect and exchange information. They verify the identity of a server, organization, or website.

Users can exchange data using public and private key pairs received and transferred by a reputable certificate authority (CA) using the SSL/TLS Internet-based Public Key Infrastructure (PKI). Public key certificates across insecure networks are issued, held, and revoked by this trustworthy organization.
A website that uses a secure connection provides a digital certificate to your browser when you visit it. Your web browser compares The issuer to a trusted Certificate Authorities (Root CA) list. The client browser determines if a trusted Root CA signed the issuing CA certificate if a match cannot be found. Until it notices a trusted root certificate or reaches the end of the trust chain, the chaining engine of the browser keeps checking the identity of each certificate’s issuer.
The primary objective of the chain of trust certification is to show that a particular certificate comes from a reliable source. Based on interface trust indications, the user will determine if the website is secure, if the certificate is valid, and connect back to a Root CA in the client browser’s Trust store.
Fundamental Entities of Chain of Trust
Root, Intermediate, and End-entity are the three fundamental entities that make up a reliable chain of trust. Let’s discuss each in more detail.
Root Certificate: The Secure Foundation
A Root certificate is a secure self-signed certificate that complies with X.509 requirements. Web-based clients and apps can verify a trustworthy source has validated the end entity’s identification due to a multi-level hierarchical chain of trust.
All certificates signed with the Trust Anchor private key will also be compromised, as would all certificates issued by that CA if the Trust Anchor private key is compromised. As a result, the CA will issue fresh certificates to each intermediate CA and end-entity in the certificate chain. Instead, the Root Authority will create one or more intermediate CAs and sign to issue certificates and connect them back to the Root CA.
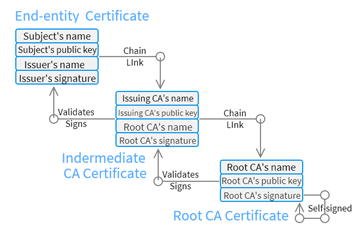
Intermediate Certificate: The Issuing CA
An SSL certificate chain nearly typically includes at least one intermediary certificate. They offer a crucial connection that enables the Root CA to extend its trustworthy reputation to end-entities that would not otherwise be trustworthy.
It is an intermediary for the server certificate and secure root certificate issuing CA. This offers an additional layer of security by enabling the Root CA to be kept securely offline.
Explicit trust is always placed in the root CA. Over 100 trustworthy root CA certificates are pre-installed on every operating system, third-party web browser, and customized application. Non-root certificates are implicitly trusted and do not have to be provided with an operating system, web browser, or certificate-aware application.
End Entity Certificate: Server Certificate
Security, flexibility, and compliance with CA criteria are all provided by server certificates. Certificates do not imply that the subject is reliable, legitimate in his business operations, compliant with all applicable laws, or secure to run business with.
On a Certificate Signing Request form, the end entity gives crucial data to the issuing CA. A reputable CA then signs and issues the certificate, attesting to the accuracy of the data at the time of issuance. If the certificate is not checked and signed, the SSL connection to the server will fail.
In certain circumstances, Server Certificate Subscribers are not the participants in the certificate; this depends on the needs of the certificate environment. The certificate given to an organization for its employees merely attests to the fact that the CA has verified the required data from a single representative of that organization, not from all its workers.
For Instance, the “Chief Information Officer” is a distinct individual, although the “IT Staff Member” is not; therefore, a Root CA may issue certificates that identify the role instead. When non-repudiation is necessary, this kind of role-based certificate is utilized.
When several subscribers share a Private Key certificate, the Root CA may issue a group certificate. The CA must keep track of all Subscribers with access to the private key and account for the time each Subscriber controls the key if many entities work in the same capacity.
Why is it Essential to have Certificate Authorities?
The following justifies the importance of certificate authorities:
Secure Transactions:
By verifying companies, domains, and websites, certificate authorities play a crucial role in digital security. Doing this reduces the chance of theft or fraud by ensuring that transactions between parties are reliable and transparent.
Improved Security:
For Instance, a certifying authority could offer its users certificates to log into a site. Issuing individual certificates may be significantly safer than using passwords since private certifying authorities frequently serve internal networks with limited users.
Conclusion
To ensure the authenticity of the client and the organization, a certificate authority is essential in facilitating secure communication and creating confidence between a user and a resource.
For a comprehensive list of recommendations for designing a CA hierarchy and the level of business impact at which you should consider applying them, please visit Certera.com, an advanced Certificate Authority that provides affordable Digital Certificates and the most recent and effective Cyber Security Services.
FAQ’s
What is the CA Certificate?
CA certificate is known as a digital certificate issued by a certificate authority (CA). For trusted roots, the CA checks trustworthy certificates. Trusted roots serve as the foundation upon which certificates’ chains of trust are constructed. When a CA root is trusted, all certificates generated by that CA are also trusted.
What is the Role of a CA in a PKI?
In addition to issuing digital certificates and assisting in developing trust between online communicators, the CA verifies domain names and organizations to confirm their identities and manages certificate revocation lists.
What Distinguishes PKI and CA from One Another?
A PKI’s primary objective is to connect a key to an object securely. A certificate authority (CA) is the recognized entity that signs the document, tying the device’s key to it. For signing these documents, the certificate authority also has a cryptographic key that it can employ. Certificates are the name given to these documents.
