Man-in-the-middle (MITM) attacks are becoming more common nowadays. Installing software and apps on smartphones is becoming more popular than ever, giving criminals an easy way to get your information.
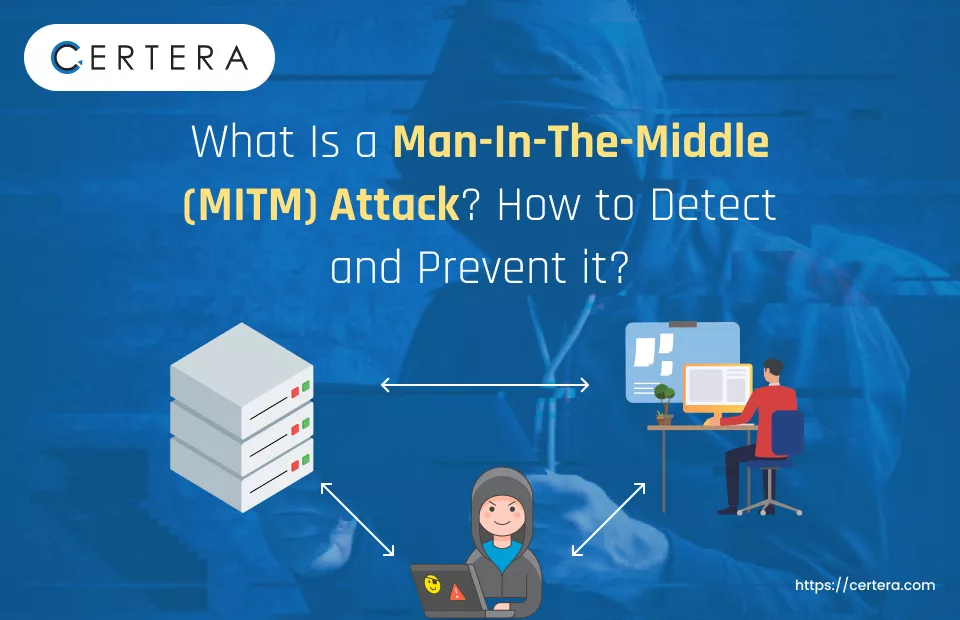
The man-in-the-middle (MITM) attack is a type of cyberattack that allows hackers to gain access to data or communications between two parties (such as an individual and an application or a client and a server). They can pretend to be one party to mislead the other into thinking they are interacting with each other, or they could alter or steal the data.
Criminals can use the MITM attack to obtain sensitive data, including payment details and login credentials. It serves as a typical port of entry for several expensive cyberattacks.
These attacks are particularly successful in settings lacking security norms like authentication and encryption.
Read on to learn more about man-in-the-middle attacks, including what they are, how they work, alert signs to look out for, and how to secure yourself.
What is a Man-in-the-Middle Attack?
“man-in-the-middle” (MITM) attacks occur when a hacker intercepts data transmitted between two devices, usually a host server and a computer or mobile device running a web browser.
Hackers usually employ Man-in-the-Middle (MITM) attacks to get payment card or bank account information and login passwords. To infect your device with malware and corrupt it, cybercriminals could also attempt to modify the data being transferred.
Networks with inadequate security, mainly accessible public WiFi networks, are vulnerable to MITM attacks. Even amid an MITM attack, everything may seem perfectly normal to the end-user on their computer or mobile device.
Your internet connection is compromised by the criminal, who then uses it to gather information on your online activity. Until they do an act, you will never know the offender exists.
The interception phase and the decryption phase make up the MITM attack.
The attack begins with an interception. To prevent you from reaching your targeted location, the cybercriminal tries to intercept your internet activity during this phase.
During the decryption stage, the criminal discreetly decrypts encrypted connections and decodes stolen data to make it appear that no monster is behind it.
An MITM attack may be launched against a person or a company. This kind of attack is used by criminals to get access to a company’s IT network so they may swiftly do extensive harm.
The objective is to get proprietary information about your business or your personal information, including bank account numbers and passwords. Criminals can utilize this information to commit financial or identity theft, utilize their accounts to make fraudulent transactions, or cause chaos.
Example of MITM Attack
To give you an example, imagine Eve listening in on Alice and Bob’s conversation but being upfront. Eve might inform both Alice and Bob that she is Bob.
Alice would disclose her side of the discussion to Eve, but she would think she was speaking to Bob. After learning more from this, Eve could change her response and send it to Bob, who would assume he is speaking with Alice. Eve manages to subtly take over their discourse.
How do MITM Attacks Work?
MITM attacks can take many forms, but they always include an intruder intercepting a communication channel, rerouting the data to the attacker’s intended spot, and, if required, decrypting the data. These attacks frequently occur during a user’s attempt to enter a service or website.
Cybercriminals insert themselves into internet communications or data transfers during MitM attacks. By disseminating malware, the attacker can quickly access the user’s web browser and the data it transmits and receives during transactions.
MitM attacks are primarily directed at online banking and e-commerce websites that need safe authentication using public and private keys. They allow attackers to access sensitive data, including login passwords.
Data interception and decryption are the two steps often used to carry out these attacks. In a data interception scenario, an attacker intercepts a data transmission between a client and a server.
To intercept data, establish a connection to the website, and function as a proxy to read and insert bogus information into the conversation, the attacker deceives the client and server into thinking they are communicating with one another.
A typical data interception method consists of the following phases:
- When a user visits a website utilizing the Hypertext Transfer Protocol (HTTP) or an insecure public hotspot, for example, an attacker can detect any possible harmful network activity by installing a packet sniffer.
- The attacker gets the user’s information after they log on to the compromised website and uses it to send them to a fraudulent one.
- The attacker can access all the original website’s user resources by using the spoof website, which imitates the real one and collects all relevant user data.
The intercepted data is decrypted during the decryption stage. This crucial stage allows the attacker to interpret the data and use it for their benefit; they may then steal identities or interfere with company operations, for example.
What are the Types of MITM Attacks?
Cybercriminals utilize several techniques to launch MitM attacks to get devices and sensitive data:
Email Hijacking
Cybercriminals hijack the email accounts of banks, financial institutions, or other reliable businesses that have access to private information and money, as the name of the attack indicates. Attackers can keep an eye on client correspondence and transactional data while they’re inside the bank.
Recommended: What is Email Spoofing? Definition, Example & Prevention
More dangerous situations involve attackers impersonating the bank and sending emails to clients telling them to give their login information again or, worse, to transfer funds to an account they own. Social engineering, or gaining the victims’ confidence, is essential to the effectiveness of this MITM attack variant.
DNS Spoofing
The technique of utilizing altered DNS records to route legitimate online traffic to a spoof or fake website that is intended to appear and feel like a website that people are likely to recognize and trust is known as DNS cache poisoning, often referred to as Domain Name System (DNS) spoofing.
Including all spoofing tactics, attackers trick users into unintentionally logging into the fraudulent website by persuading them to do specific actions, including paying a charge or transferring money to a specified account. The attackers take as much information from the victims as they can.
ARP Cache Poisoning
An internet layer address can be associated with a link-layer address, such as a media access control (MAC) address, using the Address Resolution Protocol (ARP), a communication protocol. The ARP is crucial because it converts the link-layer address to the local network’s Internet Protocol (IP) address.
In this scam, the cybercriminal uses fraudulent data to mislead the victim’s computer into believing that the fraudster’s machine is the network gateway. As a result, once the victim’s PC is online, it practically routes all its network traffic through the malicious actor rather than the actual network gateway.
After this, the attacker uses the redirected traffic to examine and obtain all the necessary data, including personally identifiable information (PII) saved in the browser.
Stealing Browser Cookies
A cookie is a small piece of data kept in computers. Data gathered by a web browser and saved locally on a user’s computer is called a browser cookie, sometimes called an HTTP cookie. Websites may improve user experience by remembering information using browser cookies.
For instance, when cookies are enabled, users may avoid repeatedly entering the same information on a form, such as their first and last names.
Browser cookie theft must be coupled with another MITM attack method, such as WiFi eavesdropping or session hijacking, to be effective. Using one of the other MITM approaches, cybercriminals can access a user’s device, steal browser cookies, and use an MITM attack’s full capabilities.
By accessing browser cookies, attackers can obtain passwords, credit card numbers, and other private information that users frequently save.
Session Hijacking
A sort of MITM attack known as “session hijacking” occurs when an attacker waits for the victim to check in to an application, such as email or banking, before stealing the session cookie. After that, the attacker logs in to the victim’s account using the cookie, but from the attacker’s browser.
Recommended: Session Hijacking: A Detailed Guide for Safeguarding Your Online Interactions
A session is a data point that denotes a brief flow of information between two devices or between a user and a computer. Because sessions identify users who have signed in to a website, attackers exploit them. Attackers must act fast, though, because sessions end after a predetermined period—which may be as little as a few minutes.
HTTP Spoofing
The HTTP protocol is the physical manifestation of safe online communication. A website with HTTPS is secure and reliable. During an HTTPS spoofing attack, a browser session is switched to an insecure or HTTP-based website without the user’s knowledge or agreement.
Cybercriminals may monitor user behaviors and steal disclosed personal data through this redirection.
How to Detect an MITM Attack?
Man-in-the-middle attacks, which are designed to be concealed, can be challenging to detect. There are several ways to tell if you’ve been the target of an MITM attack.
Monitoring Network Activity:
Tools for packet analysis and network monitoring, such as Wireshark and tcpdump, can assist in looking for unusual traffic in your IT environment.
SSL/TLS Certificate Verification:
Users can confirm they communicate with the proper company by checking SSL certificates and other authentication mechanisms.
Setting up Antimalware Software:
Antivirus and antimalware software can help identify unapproved programs and code that a man-in-the-middle attacker has inserted.
Searching for Unwanted Communication:
If you notice odd or unexpected aspects of the messages you receive, such as their timing or content, you could correspond with an MITM attacker.
How to Protect Organizations from MITM Attacks?
Follow the below tactics and protect yourself from this attack.
Implementing Multi-factor Authentication and Strong Password Regulations:
When an attacker can bypass an IT system’s security measures and pretend to be a genuine user, they can launch many MITM assaults. It’s far more difficult for MITM attackers to employ this strategy when users must use multi-factor authentication (MFA) and create strong passwords.
Practical Access Point WEP/WAP Encryption
Wireless access points with robust encryption stop unauthorized individuals from connecting to your network just by being nearby. An attacker may start a man-in-the-middle attack by brute-forcing their way into a network because of a poor encryption technique. The stronger the encryption implementation, the safer it is.
Employ Safe Communication Methods
The use of SSL/TLS and HTTPS has grown significantly in popularity. According to the company’s transparency report from January 2022, 95% of Google websites use HTTPS.
Given man-in-the-middle tactics like HTTPS spoofing, it needs to be more than just activating HTTPS on the pages that need authentication. You can access crucial services even with the smallest of windows.
Additionally, organizations must consider setting up HTTP Strict Transport Security (HSTS). DNS over HTTPS is another solution that stops DNS hijacking, which encrypts DNS queries.
Using S/MIME and a Robust Patch Management System will help Prevent the Attacks
The lack of updated systems among individuals and organizations is a vulnerability that cybercriminals exploit. Patches are necessary to fix vulnerabilities when they are found.
A patch management system is essential since a system needs many servers, programs, and hardware to function.
Encrypt your Every Email and Communication with Reputed S/MIME Certificates ~ Starts at $9.49/Yr
Secure/multipurpose internet mail extensions, known as S/MIME, encrypt emails in transit and at rest. S/MIME allows the use of a digital certificate to sign emails. Each user is assigned a unique certificate to verify the sender’s legitimacy.
Set Up a Mechanism for Managing Certificates
An automated certificate management system is the most effective defense against a Man-in-the-Middle (MITM) attack. The lifespan of each digital x.509 certificate inside the system is tracked and maintained by a certificate management system.
Reputable certificate authorities like Certera, which offers sophisticated and reasonably priced SSL certificates, make obtaining SSL certificates simple.
~ Starts at Just $3.99/Yr
Manual monitoring is prone to human mistakes, and enterprise networks may house thousands of certificates. All the certificates housed in the system are found by an automated system, which offers a simple method to access them. As active certificates are about to expire, it analyzes them and notifies users. It also handles revocation or remediation.
Also Read: Manual vs. Automated SSL Certificate Management
How Do MiTM Attacks Get Prevented by SSL?
Installing an SSL certificate, which consists of both the SSL protocol and the Certificate itself, activates the public critical infrastructure.
The transition to HTTPS, which protects all online and electronic communication, is made possible via the SSL protocol. The private key is the only thing that can create a legitimate connection with a matching certificate.
Based on the Certificate Authority (CA) architecture, the Certificate verifies the owner’s identity and dependability.
MitM attacks and other external interference are stopped after an SSL certificate is installed on the server. The hacker doesn’t have the private key, so even if he intercepts the data, he can’t decode it. The server is the only owner of the private key.
The hacker must utilize its Certificate to deceive the client into thinking he is the “Server.” The hacker cannot create any reliable SSL Certificate to appear as though he owns it, as respectable CAs often provide SSL Certificates.
The browser will mark the Certificate as “Invalid” if it attempts to counterfeit it and supply its private key, destroying the CA’s signature from the Certificate.
The hacker will be compelled to obtain a fraudulent certificate that has yet to be verified by a trustworthy CA. Once more, any contemporary browser would undoubtedly identify and label this Certificate as “Not Secure.” Thus, an SSL certificate prevents a MitM attack from occurring.
Takeaway
SSL successfully reduces the danger of Man-In-The-Middle attacks by encrypting communication channels, authenticating server authenticity, and ensuring the integrity of sent data. This creates a safe and reliable connection between the client and the server.
As previously suggested, a strong blend of procedures, standards of excellence, and tools could effectively prevent man-in-the-middle attacks. So, always be mindful of cybersecurity while working with SSL certificates.