How to Combine Multiple Intermediate Certificates?
You must have observed the complexities when navigating through Certificate Authorities and their Intermediate Certificates. Similar to the channels of secure connections, these certificates often need to be spoken more due to the limitations of browsers and mobile devices.
These limitations, sometimes constrained by the size of the certificates, result in a gap that casts a shadow of “Untrusted” over the connection.
The SSL Handshake, a virtual handshake of trust between your device and the server, becomes complete with the exchange of these Intermediate Certificates.
To stabilize these connections, perform the SSL Installation, where the missing link is the Intermediate Certificate provided by the Certificate Authority.
The Certificate Authorities install not one but multiple Intermediate Certificates. Yet, the server’s canvas is often primed for a solitary stroke, accommodating only a single Intermediate Certificate entry. In this delicate deadlock, the webmaster articulates the distinct Intermediates into a singular “.CRT” opus, aptly christened the “CABundle.”
In these certificates, we find a testament to particular security measures. As we go through the layers of cryptography, a more apparent picture emerges, revealing the need to transform certificates into a trusted connection.
Prerequisites of Multiple Certificates Combination
Gearing up for melding multiple Intermediate Certificates demands a precise set of tools and a touch of digital finesse. Your arsenal for this endeavor is simple yet pivotal: your certificate files.
While the specific composition of these files might sway depending on the Certificate Authority you’re partnering with. The underlying principle remains steadfast.
Within the confines of the “.zip” package bestowed upon you by the Certificate Authority lies a meticulously curated assortment of files, each holding a distinct role in the security ensemble. It’s akin to assembling a jigsaw puzzle where each piece is imbued with significance.
Now, let’s get into the gallery of these digital assets.
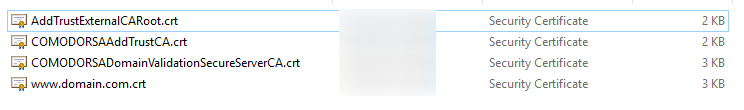
The files bearing names like “AddTrustExternalCARoot.crt,” “COMODORSAAddTrustCA.crt,” “COMODORSADomainValidaitonSecureServerCA.crt,” and the familiar “www.domain.com.crt” grace this collection. The magnetism of emboldened text directs our gaze to the stars of this showcase — the Intermediate Certificates that are the heartbeats of secure connections.
Their unified “.crt” relation is the essence of the task. Just as skilled hands combine musical notes to craft a harmonious composition, you’re called upon to weave these seemingly disparate certificates into a single security fabric. Your effort will be a “CABundle,” a convergence of trust that elevates the connection from the every day to the secure.
So, you’re not merely combining certificates; you’re building encryption where every move counts and security is paramount.
All About a Root and an Intermediate Certificate
In secure online communication, the trust hierarchy has the significance of root and intermediate certificates. These certificates serve as pivotal components within the SSL issuance framework, contributing to the establishment of a secure and encrypted connection between users and servers.
Hierarchical Importance
Central to comprehending the divergence between root and intermediate certificates is their hierarchical position within the chain of trust. The intricate web of intermediate and subsequent server certificates would continue to exist with the foundational root certificates.
Signature Sequence
A pivotal distinction lies in the digital signature sequence. Root certificates employ their private keys to sign intermediate certificates, imbuing them with credibility. Conversely, intermediate certificates utilize this signed status to sign other intermediates further and, ultimately, the server certificate itself.
Process of Issuance
In the intricate choreography of certificate issuance, the Certificate Authority (CA) orchestrates the signing of root certificates, subsequently integrating them into the root stores of diverse applications and software.
This strategic deployment of intermediate certificates as intermediaries fortifies the security of root certificates, fostering an additional layer of protection between the root and server certificates.
Lifespan Dynamics
The lifespan of certificates unfolds as a dynamic interplay. Root certificates boast longevity, extending their validity from a decade to two, rendering them stalwart sentinels of the SSL ecosystem.
Conversely, the intermediate certificates, mindful of security imperatives, sport a comparatively shorter shelf life. As one traverses the hierarchy of trust, the temporal validity of SSL certificates diminishes, culminating in end-user certificates with a modest one-year existence.
Secure Abodes
Intricacies in certificate security manifest through divergent storage protocols. Endowed with paramount significance, root certificates are enshrined within impenetrable hardware security modules.
These modules stand fortified behind formidable barriers, monitored ceaselessly by vigilant guardians. Intermediate certificates find their abode within server installation directories, a testimony to their intermediary role.
Distinguishing the Certificates
Discerning between root and intermediate certificates emerges as a critical task. A fundamental criterion involves perusing the certificate itself. If the “Issued to” and “Issued by” fields mirror each other in identity, the certificate assumes the stature of a root certificate.
This unity is predicated on the exclusive authority wielded by trusted certificate authorities in issuing root certificates. Conversely, if disparities emerge in these fields, the certificate is intermediate.
An alternative differentiation lies within the Certification Path. This path unfolds with the root certificate reigning supreme at its zenith, followed by the sequential arrangement of intermediate and server certificates.
Additionally, the temporal dimension surfaces as a discriminator. Endowed with extended validity, root certificates bear dates that contrast with the relatively transient intermediate certificates.
Combining Multiple Intermediate Certificates Process
This procedure transforms fragmented security components into a cohesive shield of protection. To embark on this journey, follow these detailed steps:
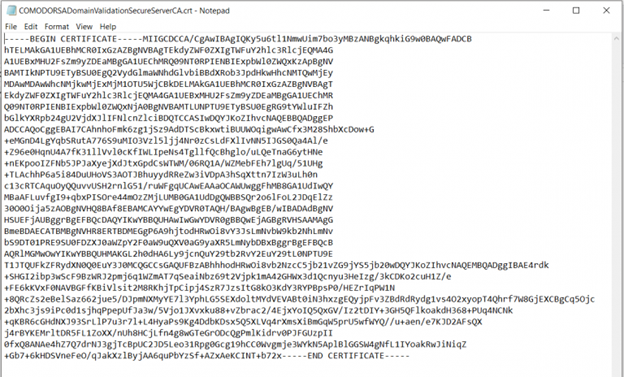
Discover the First Intermediate:
Begin by right-clicking on the “COMODORSADomainValidationSecureServerCA.crt” file. Open this certificate using a Word Processor application, like Notepad or a Text Editor. As you do so, your screen should mirror the screenshot provided. To introduce a clear differentiation, insert a line break at the end of the document by pressing the “Enter” key.
Explore the Second Intermediate:
Extend your digital canvas by opening the “ComodoRSAAddTrustCA.crt” file as before. Once the file is unveiled, execute a copy-and-paste maneuver, transferring all its contents to the end of the first Intermediate Certificate. Your result should reflect an artful blend of certificates, indicated by the appearance of “END CERTIFICATE” and “BEGIN CERTIFICATE.”
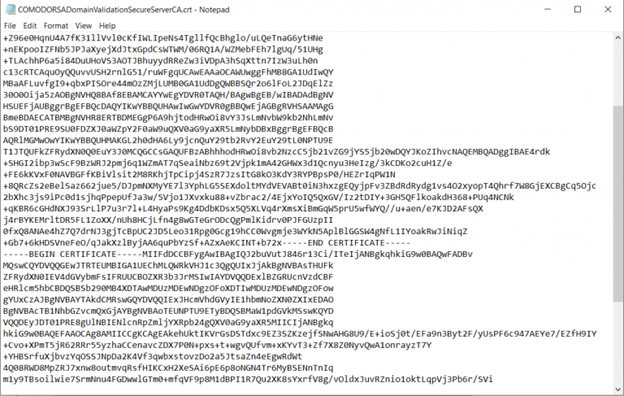
Enveloping into One:
With finesse, merge the two Intermediates into a singular entity. If the amalgamation mirrors the earlier exemplar, you’re poised for the final step. Save this culmination of security prowess with an easily recognizable name, such as “www.domain.com.CABundle.crt.” This nomenclature ensures effortless retrieval during the installation odyssey.
Armed with this united front of certificates, your team is primed to embark on the SSL Certificate installation journey. This comprehensive step brings you closer to strengthening your digital domain with robust security, ensuring a smoother and safer online experience.
Looking for a Quick SSL Installation? Certera.com offers hassle-free SSL Installation Support for your Websites through a dedicated and professional team of experts.
– Get SSL Installation Services Starts at Just $29.99

